I am worried that there is not really a benefit of doing that, just more noise and energy consumption.
Energy consumption is essentially the same, as it’s using the same radios.
For what it’s worth, I have several SSIDs, each on a separate VLAN:
- my main one
- Guest. Has internet access but is otherwise isolated - Guest devices can’t communicate with other guest devices or with any other VLANs.
- IoT Internet: IoT and home automation devices that need internet access. Things like Ecobee thermostat, Google speakers, etc
- IoT No Internet: Home automation stuff that does not need internet access. Security cameras, Zigbee PoE dongle (SLZB-06), garage door opener, ESPHome devices, etc
(to remotely access home automation stuff, I use Home Assistant via a Tailscale VPN)
Most of these have both 2.4Ghz and 5Ghz enabled, with band steering enabled to (hopefully) convince devices to use 5Ghz when possible.
This is on a TP-Link Omada setup with 2 x EAP670 ceiling-mounted access points. You can create up to 16 SSIDs I think.
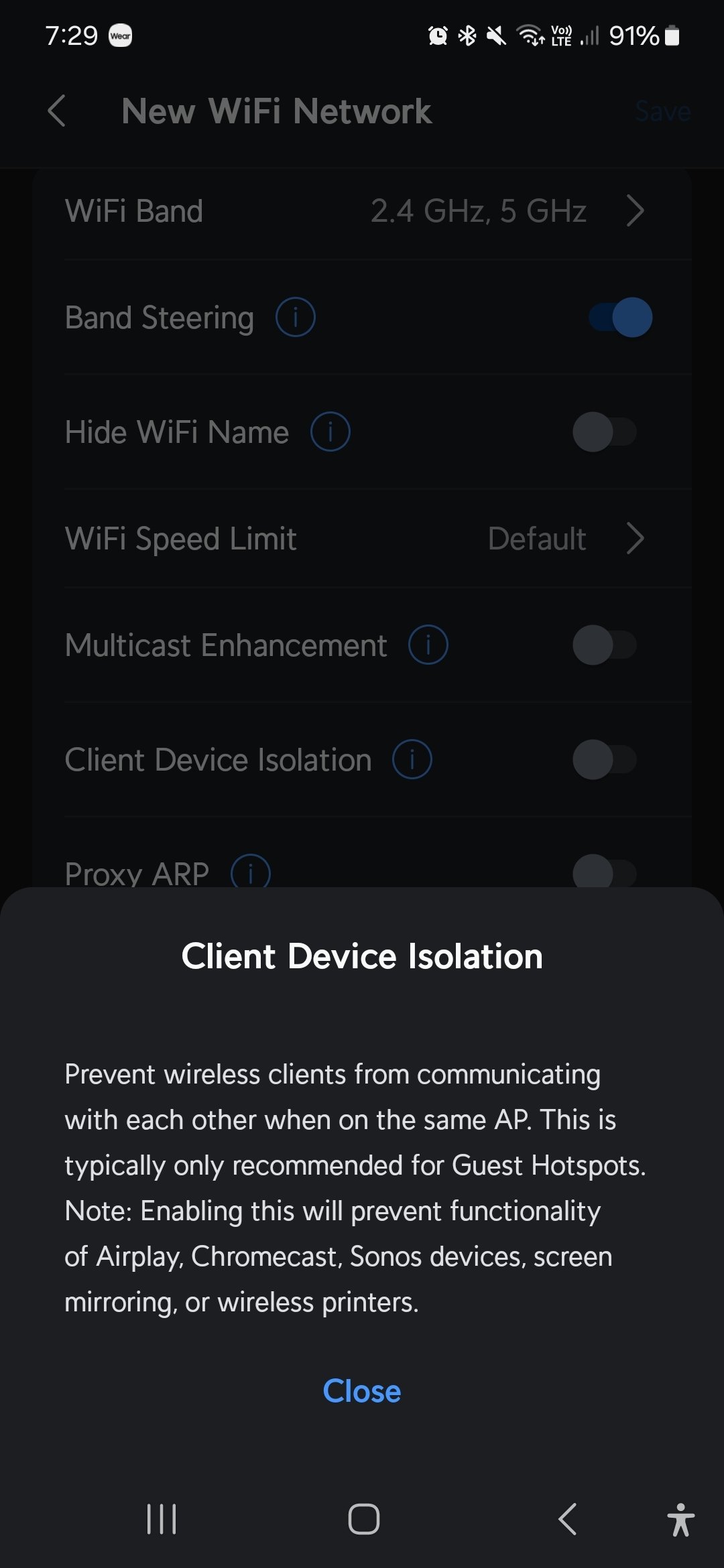
Guest devices can’t communicate with other guest devices
How do you accomplish this isolation since they’re on the same subnet/broadcast domain? Is it a feature of the hardware you’re using?
A lot of access points, even consumer-grade ones, have this option. It’s usually accomplished via predefined firewall rules on the access points themselves.
Consumer-grade access points usually let you have just one isolated guest network, whereas fancier ones (Omada, Unifi, Ruckus, Aruba, etc) usually let you enable isolation for any SSID (ie the “guest network” is no different from any other SSID)
Isolated guest networks I get, but isolating guests from other guests on the same subnet/isolated net is what I haven’t seen.
The APs know who the Wi-Fi clients are and just drops traffic between them. This is called client/station isolation. It’s often used in corporate to 1) prevent wireless clients from attacking each other (students, guests) and 2) to prevent broadcast and multicast packets from wasting all your airtime. This has the downside of breaking AirPlay, AirPrint and any other services where devices are expected to talk to each other.
If there’s an option on the AP to not permit link local routing within a vlan/ssid, that will force all traffic up to the firewall. Then you can block intrazone traffic at the firewall level for that vlan.
I’ve seen this in Meraki hardware where it’s referred to as “client isolation”. Ubiquiti might be able to do this too.I used to have a Netgear Nighthawk router/AP I bought from Costco, and if I remember correctly, its guest network automatically isolated guests from other guests. This router didn’t support VLANs so I think it was just a bunch of firewall rules.
Unifi out of the box settings.
For Unifi devices you setup a Virtual Network then assign the guests to that. https://help.ui.com/hc/en-us/articles/115000166827-UniFi-Hotspot-Portal-and-Guest-WiFi
I’m not seeing anything there that says guests can’t see other guests - quite the opposite.
guests connected to your Hotspot Portal will be isolated from all other networks except the one they are assigned to.
Guests on this network are able to access the internet, and communicate with the UniFi gateway to obtain a DHCP lease and resolve names using DNS
I suppose a switch could be configured to prevent traffic going to other ports, which is how I would assume this would have to be done. This functionality would have to exist in the access point, I guess?
Does UniFi have a feature to isolate devices from each other on the same subnet? Seems like it would require some kind of Layer 2 routing?
It does. I have it enabled and tested. “Client Device Isolation.” It’s enabled per SSID.
Oh, neat. I’ll have to look into it.
Thanks!
Ooh I like the idea of “no Internet.” I do trust all of those devices (open source), but they could still be pwned.
That was an amazing read. Thank you.
What do you say is the use case for separating guest Wi-Fi with the more “private” stuff on your network?
As far as I understand… Basically all communications, even inside a network, are encrypted… So I guess you do that to avoid someone trying to exploit some vulnerability?
Basically all communications, even inside a network, are encrypted
LOL, oh no.
Even internet traffic isn’t encrypted by default.
Sadly TCP/IP isn’t encrypted.
I think the main benefit is that Guests devices on your network can’t find and exploit your own devices.
If you don’t trust the person, why give them access to your WiFi in the first place?
You can trust the person, without trusting their technical skills, such that they haven’t inadvertently installed malware on their own devices.
Remember that once you give the password out, they likely have the password from now on. They will always have access until you change the password.
No, a lot of local traffic is not encrypted, especially residential. No, residential probably doesn’t use much authentication or separation of privileges.
I don’t want my guests to be able to access my home server or Omada controller for example, or spread malware (their phone may have malware without them even knowing). Also, I give the guest wifi to people other than friends, like contractors. Phone reception is horrible at my house so I give them the wifi so they can use wifi calling.
I’m not sure that I understand the “more noise and energy consumption” part, since we’re still talking about the same router with the same connected devices.
But I do have multiple SSIDs on my router. One is explicitly for IoT devices, and they don’t have network access, so they are isolated from my computers, NAS, etc.
The more SSIDs being broadcast the more airtime is wastes on broadcasting them. SSIDs are also broadcast at a much lower speed so even though it’s a trivial amount of data, it takes longer to send. You ideally want as few SSIDs a possible but sometimes it’s unavoidable, like if you have an open guest network, or multiple authentication types used for different SSIDs.
Is there a measurable, real-world effect? Because if so, I don’t see it, and I can max out my router’s bandwidth pretty easily without noticing any slowdowns (this is with 30+ devices across three different SSIDs).
Are we talking main + guest network, or 2,4GHz + 5GHz, or something else?
Why would you want to do this, anyway? Or, as I as a developer regularly have to ask our sales people: what do you actually want to achieve that led you to this question?
Here’s my use-case, I’m pretty sure the first 2 are pretty common (common enough to be supported by most OEM firmware):
- main LAN
- guest LAN (isolated from “main” but can access internet)
- IoT LAN (isolated from internet, can be accessed from “main”; prevents devices from phoning home)
But you don’t need several LANs for this. This can easily done with proper routing. A can access internet and internal network addresses. B can only access internet, and C can only reach internal addresses.
I’m curious. How would you identify who’s guest and who’s not in this case?
With multiple networks it’s pretty easy as they are on a different network.
MAC whitelist.
That’s what MAC whitelists are for. Your DHCP server should be able to handle this.
Identify your friendly devices and give them one setting with everything (full subnet and correct default GW). Identfy your IoT devices, and give them another (full, or specially limited subnet mask, and fake default GW, maybe a different nameserver, too). Anything else is guest and gets a very limited subnet mask and a working default GW.
This is not the way to do it. The correct way would be multiple SSID’s with each tagged to their own VLAN.
Each VLAN has its own subnet. You can then use a zone based firewall, to allow the zones(subnets) to access each other.
You can also then apply QOS, to limit guest network speeds, prioritize LAN traffic etc.
And zone based firewalls are stateful, you can do rules such as LAN can reach IOT, but not the other way. Or IOT can only reach the IOT server, on specific ports.
I know that this would be the most secure way. But I seriously doubt that this level is necessary in a normal home network.
“Necessary” is a little ambiguous. You could argue that wifi is unnecessary for a normal home network.
My solution is the correct way and easier way. You don’t need MAC address white-list. You just have a guest SSID with DHCP on, they get the IP from the subnet in that zone. No crazy subnet hacks etc.
Can I join your guest network, sure. Let me just grab your mac address, login to the DHCP server, create a reservation with a limited subnet mask that can still see the default gateway.
Or can I connect to you guest network, sure here is the code or scan that QR code. That’s it, they’re in the guest VLAN and subnet, zoned off on the firewall and have QOS applied to not saturate the network.
For anyone reading this, please don’t follow this advice. It’s terrible and basically security through obscurity
I’m an idiot and I put emojis in my SSID and sometimes devices don’t like that but I don’t want to change everything. So there’s a guest network with no emojis
It’s more like: I know people do this, but I don’t, so I wanted to see what was the reasoning behind these things.
Then why don’t you ask the people who do this?
Emm… I did, it’s this post 😅
I’m pretty sure I don’t do this ;-) I know how routing works.
You know just enough to do it the wrong way apparently
You know how routing works, but not wireless networks apparently.
What benefit do you hope to get?
Whether it has benefits is up to you, but from a technical perspective they’re as expensive as VLANs, so basically free. It’s the same receive and transmit radio, the only difference is that it broadcasts and responds to two network names at the same time. The maximum power consumption is the same: the max the radio will pull when at full load. The minimum power consumption has to be ever so slightly more since it needs to broadcast two network IDs, but those are measured in bytes and sent a couple times a second, it’s negligible compared to the cost of just running the radio.
Separate subsets, segregated traffic. Easy to avoid crosstalk by setting channels further apart or using 2.4ghz and 5ghz
At home I have one SSID as a main wifi, and the other is guest wifi and IoT or other random devices.
Main downside is getting it setup and maintenance.
Acronyms, initialisms, abbreviations, contractions, and other phrases which expand to something larger, that I’ve seen in this thread:
Fewer Letters More Letters AP WiFi Access Point DNS Domain Name Service/System IP Internet Protocol IoT Internet of Things for device controllers NAS Network-Attached Storage PoE Power over Ethernet TCP Transmission Control Protocol, most often over IP Unifi Ubiquiti WiFi hardware brand VPN Virtual Private Network Zigbee Wireless mesh network for low-power devices
10 acronyms in this thread; the most compressed thread commented on today has 11 acronyms.
[Thread #570 for this sub, first seen 4th Mar 2024, 09:55] [FAQ] [Full list] [Contact] [Source code]
Good bot
Typically you have main and guest to isolate them You also have different networks for different bands because they use different radios (2.4GH and 5GH) with both having tradeoffs of range and speed. Some have triband as well so that you can isolate high performance devices because every device on a network increases latency slightly, and more so a radio only support one broadcast method at a time and will downgrade its self to the least common dominator for the devices connected to it.
You don’t need to have different SSIDs for 2.4 and 5 ghz. They can be the same and the device will handle the connections.
Oh what? Dope.
Yeah depending on your WI-FI device, it might even have tools to steer devices onto specific bands. But without that, the end user devices do a semi decent job. It’s basically so that if you’re connected to 5ghz with good signal, and walk to a different part of your house it can just switch over to 2.4ghz.
The big key is your hardware needs to support it. Back when “unified SSIDs” became a thing, some older 802.11n (WiFi 4) and ac (WiFi 5) devices could do it, but it was…. Weird.
If you have a newer router, especially WiFi 6 or 802.11ax it should be be to do the unified SSID.
I am worried that there is not really a benefit of doing that, just more noise and energy consumption.
If there wasn’t a benefit, why would people (and pretty much every business) do it?
I remember reading a few self hosters describing having a separate WiFi for IoT devices, on a dedicated router (opensense) so they can prevent these devices “calling home”. They are maybe other advantages like having different WiFi channels for these things
- They can’t potentially send my “real” WiFi credentials to someone who might exploit them.
- They can’t collect data on what is on my network or what I’m doing
- If one somehow has malware, they can’t harm most of my network or devices (there are well known exploits for cameras, for example)
- I can more easily limit the amount of bandwidth a poorly behaved device can use
What benefit are you looking for? It shouldn’t affect speed unless you are really hammering it. I’m assuming your talking about two networks on the same frequency (either 2.5Ghz or 5Ghz)
Lots of answers about use-cases of additional wifi networks, so I won’t go into that. I haven’t seen the downsides mentioned here, though. While technically you can run lots of wifi networks of off the same wifi router/ap, each SSID takes a bit of air time to broadcast. While this might sound rather insignificant since this is only a rather tiny bit of information transmitted, it is actually more significant than one might expect. For one the SSIDs are broadcast quite often, but also they are always transmitted at the lowest possible speed (meaning they require a lot more airtime than normal WiFi traffic would require for the same amount of data) for compatibility reasons. This is also the reason why it is a good idea to disable older wifi standards if not needed by legacy clients (such as 54 Mbit/s 802.11G wifi).
Having two networks is usually fine and doesn’t cause noticable performance degradation, having 4 or more networks is usually noticable, particularily in an already crowded area with lots of wifi networks.
I think most wifi routers segregate the two networks, so they can’t see devices on eachothers network.
Someone will surely correct me if I’m wrong in this.
I’d say that depends. Some consumer routers may have guest network and client isolation on it though I doubt most do. Higher end routers support vlans can be configured that way and could be configured in many other wise such as talking to network 1 but not 2 or 3. For instance, I have IOT vlan allowed to connect to my server vlan for DNS since I self host DNS, but my general VLAN for personal trusted devices does can’t be accessed by IOT.